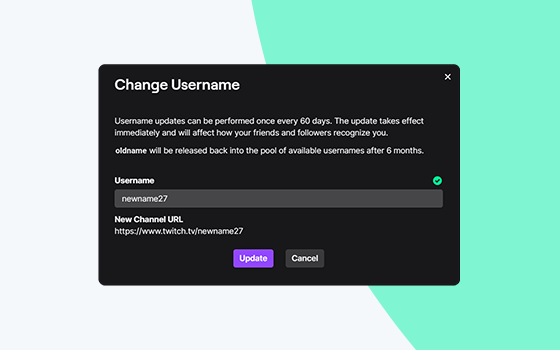
Changing your Twitch username can seem like a simple task, but it involves understanding the platform’s rules and potential impacts on your channel. Whether you're rebranding or just want a fresh identity, this guide will walk you through the entire process of updating your Twitch handle, along with important considerations and tips to make the...
Read more →